Botnets and IoT – Our Future Internet of Dangerous Things
A Dramatic Entrance
In September of 2016, a botnet called Mirai facilitated a massive distributed denial of service attack on KrebsOnSecurity, a cybersecurity blog run by Brian Krebs. This initial, dramatic entrance was eclipsed as many other high-profile targets suffered attacks, including an attack on Dyn that shut down large portions of the internet. Mirai and its successors have spurred a race to defend against a new breed of malware. Botnets present a significant threat to an internet that gets larger every day.
What is a Botnet?
A botnet, sometimes called a zombie army, is a collection of malware-infected devices that takes instructions from an outside source called a bot-herder or controller. Botnets can work in concert, pooling the computing power of many thousands of devices under the control of one leader. Cybercriminals leverage this power to conduct attacks that would be otherwise impossible for a single person, such as DDoS. A distributed denial of service (DDoS) attack is an attack on availability; numerous hosts flood a target with malicious network traffic that it cannot handle. DDoS has many variants, but the basic goal behind all of them is the same: create so much network congestion that the target becomes unusable.
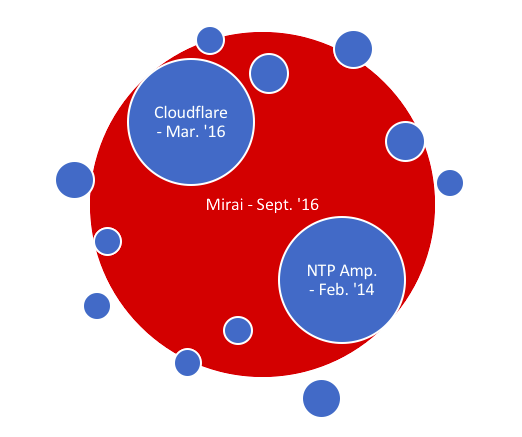
Mirai is an example of a botnet used in DDoS. While there is nothing particularly novel about this, the Mirai botnet is massive, and demonstrated a far greater attack capacity than earlier incarnations of this type of malware. Hosts involved in attacks number up to 150,000, though some estimate ten times as many infected hosts exist. Mirai is responsible for floods measuring over 1Tbps, which at the time was at least twice as large as the next largest non-Mirai DDoS attack. While most DDoS attacks last less than six hours, Mirai was used to conduct a 54-hour attack against a US college.
Mirai has altered the reigning perception of DDoS. Prior to Mirai, DDoS was once considered solely the domain of hacking amateurs because these sorts of attacks were ineffective against enterprise and had little reward potential. Internet service providers (ISP) act like a dam protecting their clients from the DDoS “floods.” The problem now is the floods are so massive that even an ISP can be overrun.
How Does the Botnet Work?
Botnets like Mirai target Internet of Things (IoT) devices, which are internet-capable consumer appliances. Webcams, routers, and other IoT devices are susceptible to infection. First, Mirai scans the internet for random IP addresses. Once it finds an active IP, it brute forces a list of generic username/password combinations, like admin/1234. If it successfully breaks-in, it reports back to the controller. The controller pushes a copy of the malware onto the target, and the lifecycle starts over.
An admin portal on the controller machine facilitates interacting with Mirai. The controller can command the infected hosts to send different types of traffic to a target. A single device generates a trivial amount of traffic, like a drop of water. But since the infected host works in concert with hundreds of thousands of other infected hosts the combined impact is enormous, like a monsoon. Removing the malware can be very difficult. For one, it is hard to detect. Most IoT devices are made with limited human interaction in mind, and a botnet will nominally impact device performance. Even if it were detected, IoT devices rarely have an interface that facilitates malware removal. The point being many infected devices will remain infected. This botnet is not going anywhere anytime soon.
The Future
While the Mirai botnet generated large amounts of media attention, its capacity has already been exceeded, and is likely to be dwarfed in a few short years. Since Mirai’s dramatic entrance onto the internet new malware of similar designs have begun appearing. It is estimated that there are currently 6 billion devices on the internet, and that in a few short years that number will explode to roughly 20 billion, with the lion’s share of newcomers comprising of IoT devices. In that world, an even more insidious worm hijacking vast numbers of IoT devices would be absolutely devastating.
The other side of this challenge is that while the internet grows larger and faster, it may also grow “thinner.” Consumers and enterprise demand ever faster connection speeds. Innovative microwave relay technology can provide exceptionally fast internet speeds. But there is an important caveat: the maximum capacity of each of these connections would likely be about 100 Gbps. Given that botnets have already achieved DDoS attacks ten times that size, a microwave-based network would be extremely susceptible to DDoS. The mere threat of DDoS might even inhibit the adoption of this advanced technology.
There are possible means of defense against this growing threat, but none of the solutions so far discovered are perfect. One idea being considered is the distributed denial of distributed denial of service (DDoDDoS). In this model, ISPs would identify the botnet aggregates, or points on the internet where the controller sends commands to the infected hosts. The ISPs would then isolate these aggregates, stopping the attack. This would require coordination among ISPs. Monetizing this defensive structure may be a challenge. Adopting an infrastructure as a service (IaaS) model, wherein an ISP rents portions of its network out to help isolate these aggregates while allowing legitimate traffic to continue, could help mitigate the future DDoS threat.
When everything is connectable, everything becomes a possible vector of attack. As it currently stands, IoT devices are not subject to many of the same laws and regulations as desktop PCs and servers. They often are not built with security in mind, and in some cases building them to be secure is not feasible. For example, while the processors could be made to prevent the device from executing unintended commands, this would be expensive and unworkable. In other words, the internet is about to become polluted with a horde of cheap, inherently insecure devices.
Just as unmitigated consumerism is wreaking havoc on the physical environment, the effects on the virtual one could also be serious. Of course, an ounce of prevention is worth a pound of cure. If we start preparing for this problem now, we will be in a much better position when it manifests. Asset owners should use their best judgment and implement IoT devices in their workplace with caution. They can take steps towards hardening their devices against botnets. The public in turn can start demanding a stronger cyber ecology now before the market is flooded with unsafe products.
Author: Louis Papa
Silent Storm Security Contributor | Security Engineer